Midnight theme
Midnight is a theme for GitHub Pages.
Project maintained by GiBoris Hosted on GitHub Pages — Theme by mattgraham
Lab 05 — Detections & Incident Response in Microsoft Sentinel 🚨🛡️
Platform: Microsoft Sentinel / Microsoft Defender XDR
Focus: Detection engineering, automation (SOAR), UEBA, and incident response
Objective
This lab demonstrates end-to-end SOC detection and response workflow in Microsoft Sentinel:
- Creating playbooks for automated response
- Building detection rules from queries
- Enabling UEBA (User & Entity Behaviour Analytics)
- Simulating attacks and validating detections
- Investigating and resolving incidents
Lab Environment
- Microsoft Sentinel workspace
- Microsoft Defender XDR
- Windows virtual machine
- Simulated attack scenarios
All activities were performed in a controlled, non-production environment.
Part 1 — Playbook & Automation (SOAR)
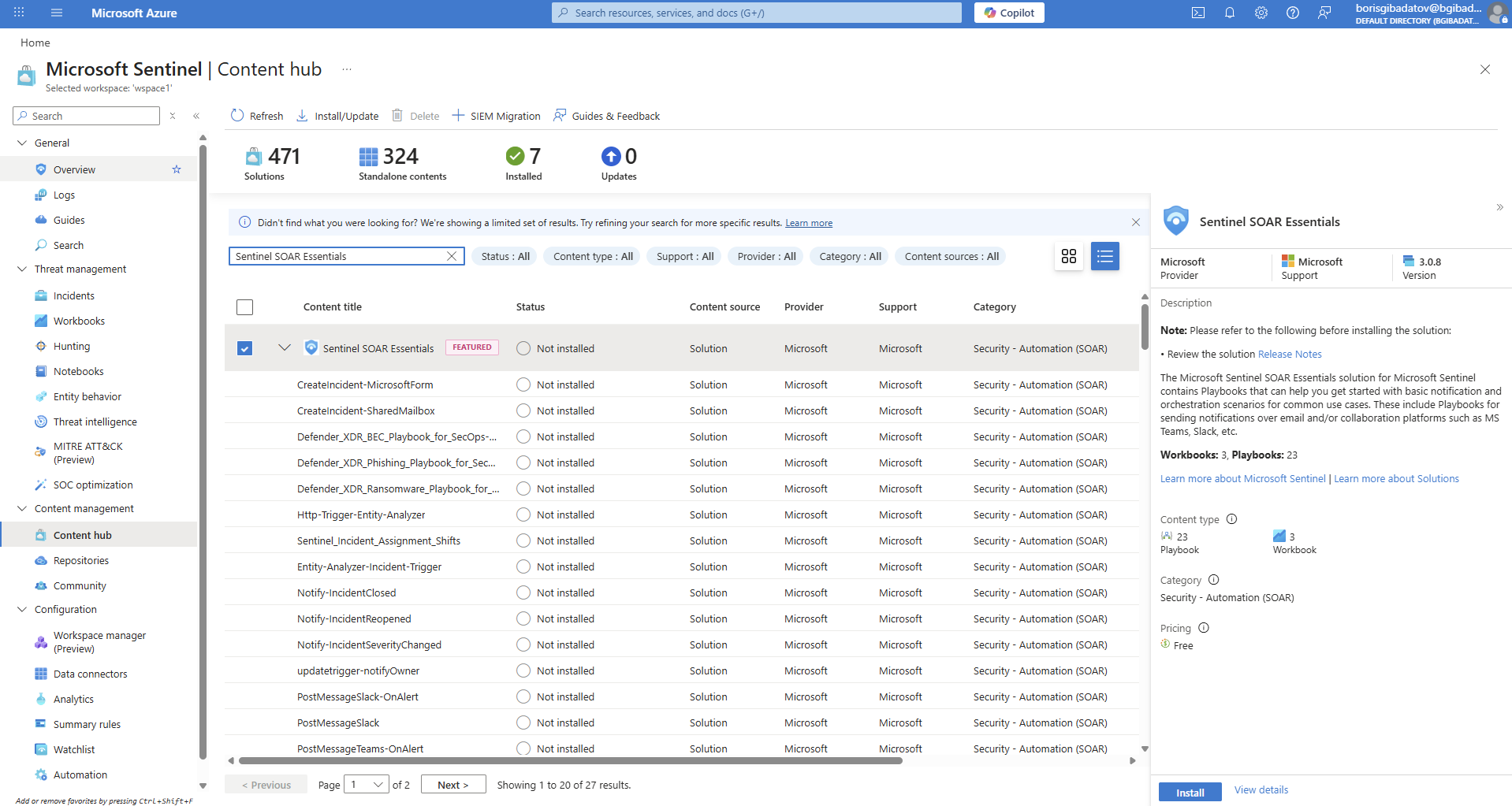
1.1 Sentinel SOAR Setup
Installed Sentinel SOAR Essentials to enable automation capabilities.
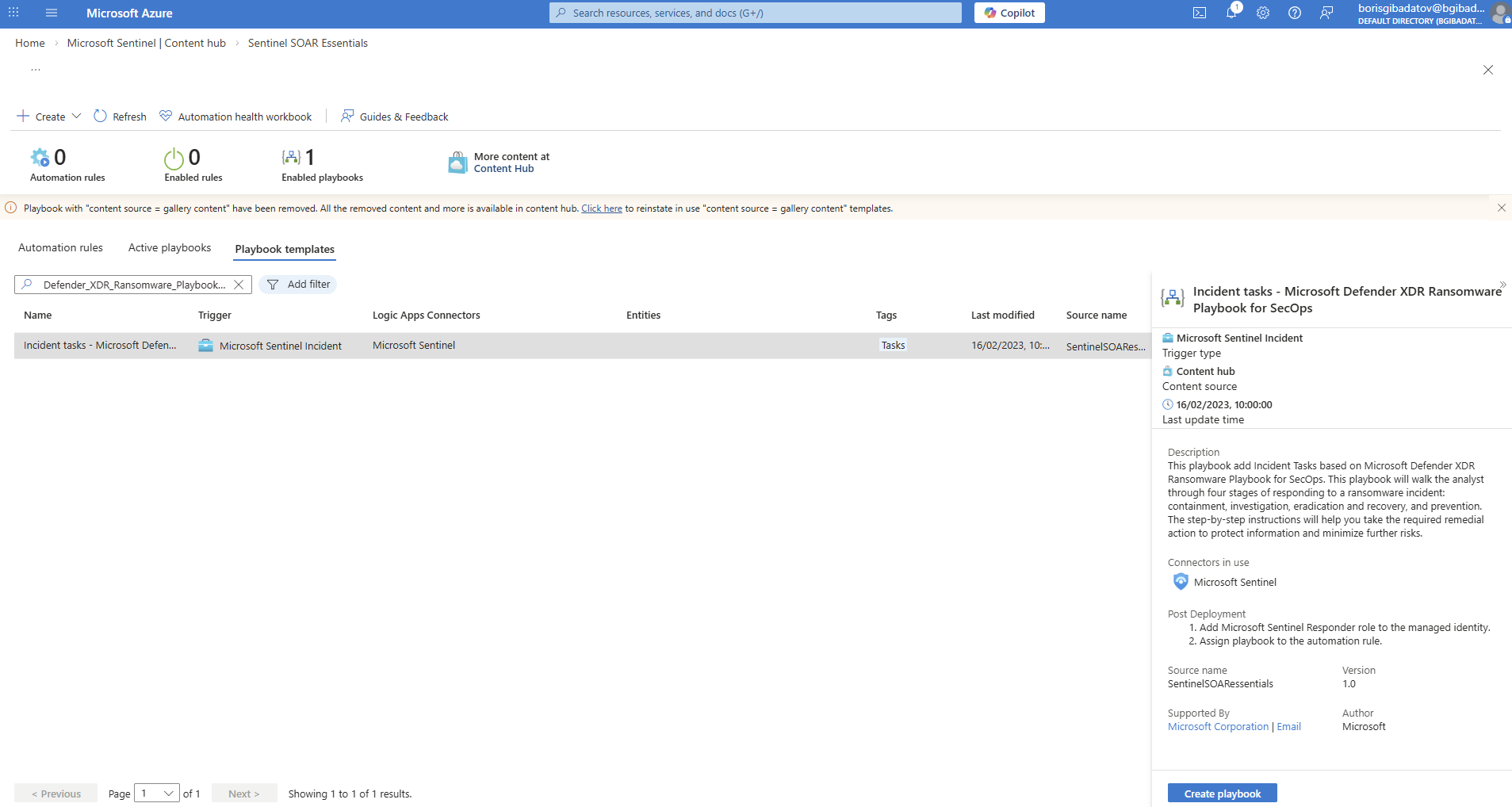
1.2 Playbook Creation
Created a playbook to automate incident response actions.
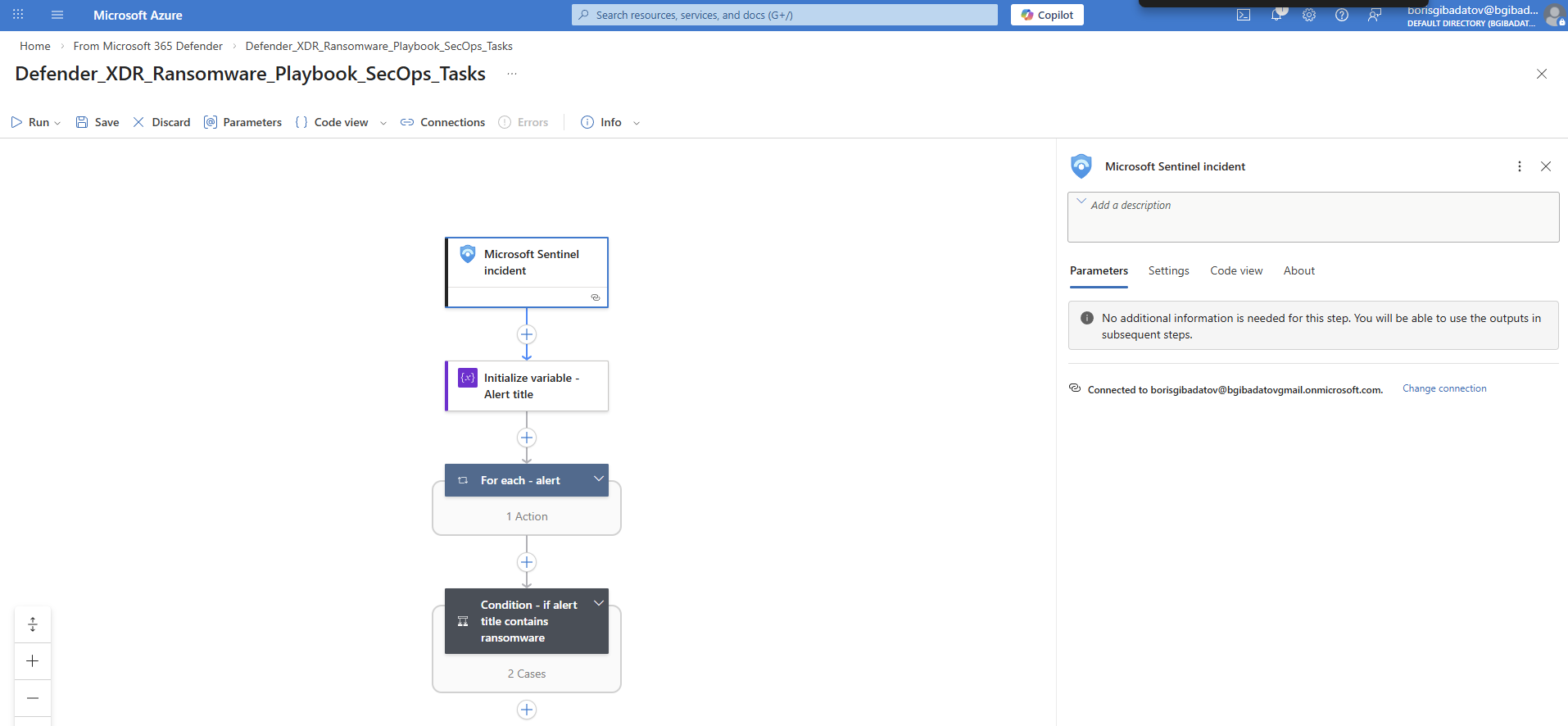
1.3 Playbook Configuration
Configured connections and permissions required for playbook execution.
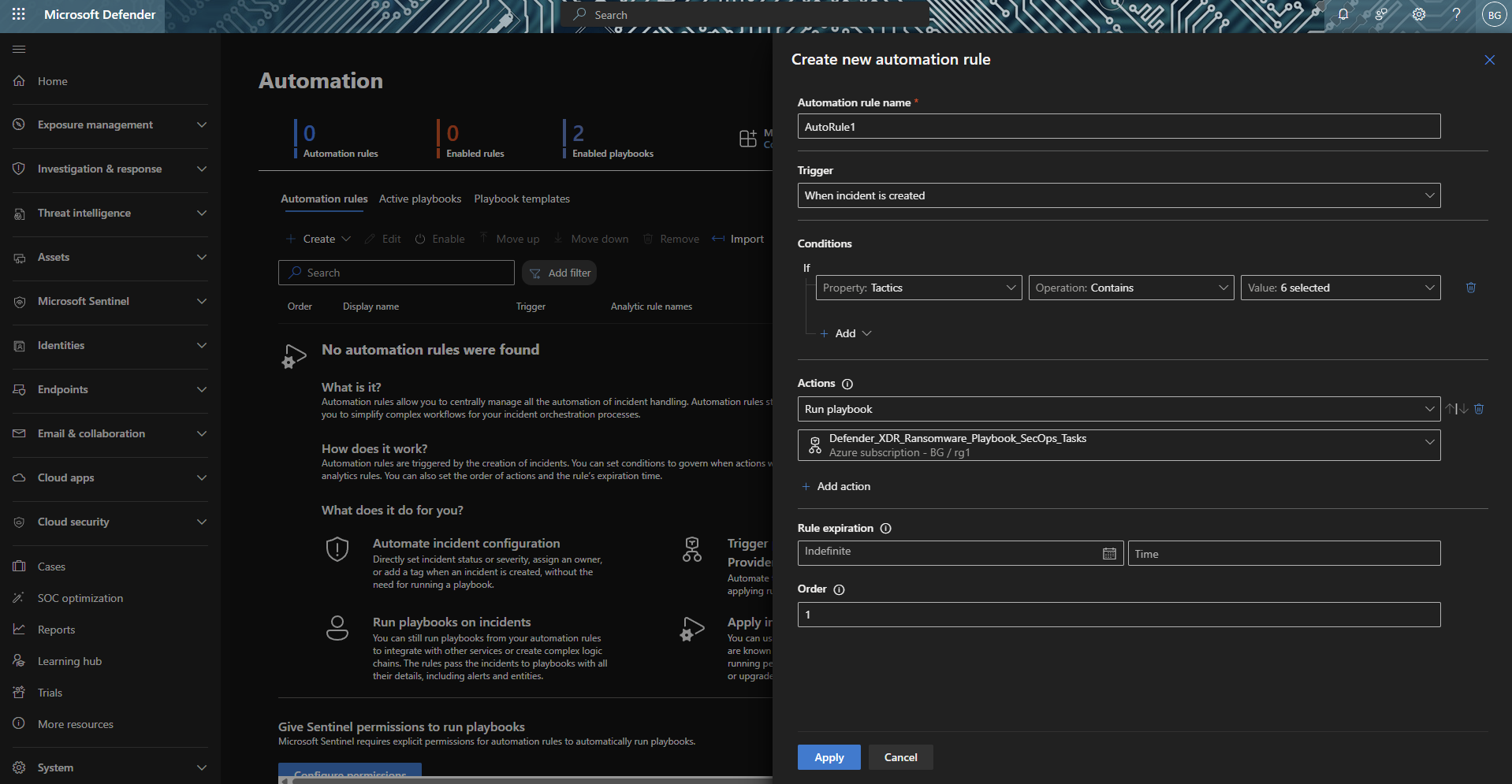
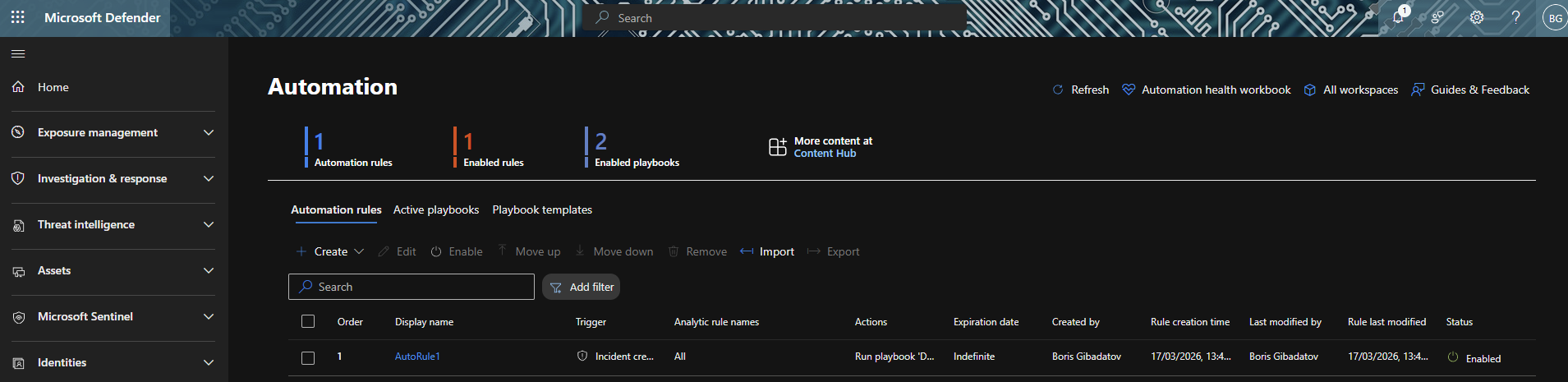
1.4 Automation Rule
Created an automation rule to trigger the playbook upon incident creation.
Part 2 — Scheduled Analytics Rules
2.1 Rule Creation
Created a scheduled query rule to detect suspicious activity.
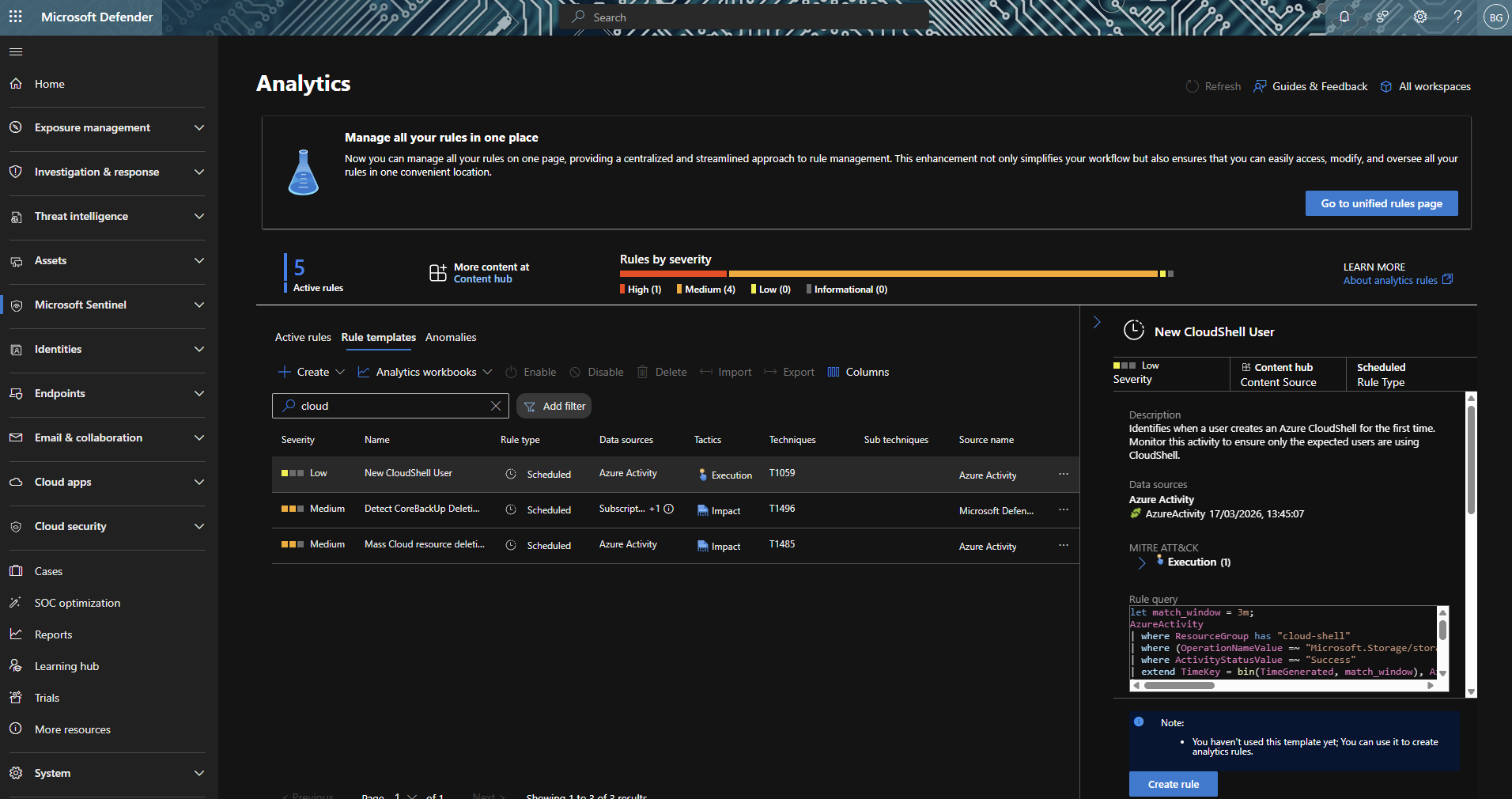
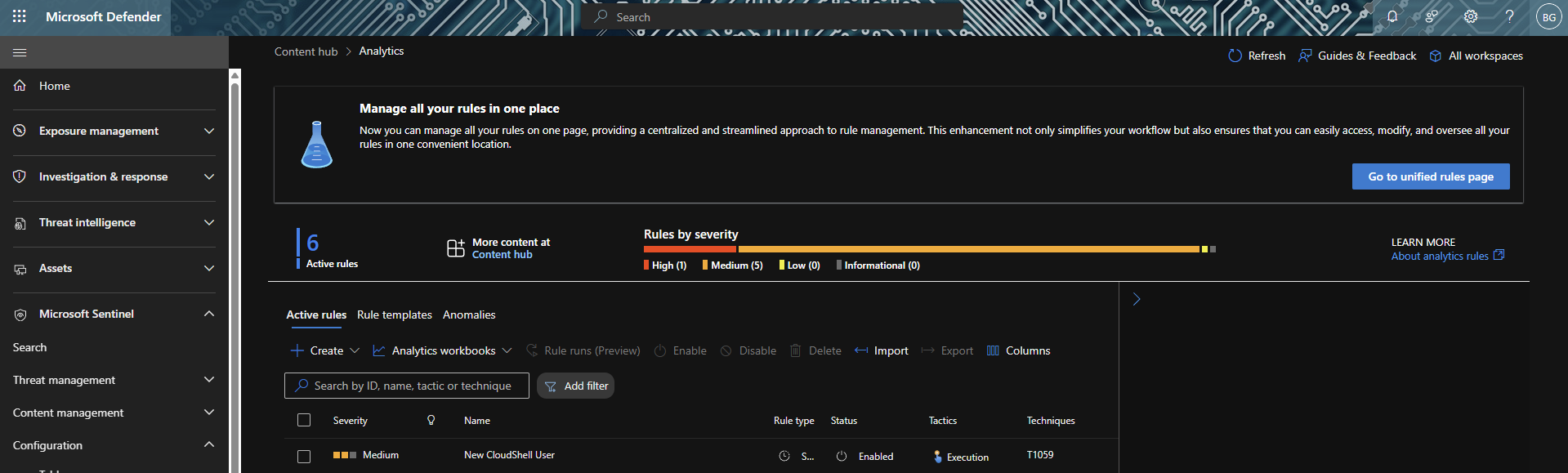
2.2 Rule Validation
Verified that the rule is active and running.
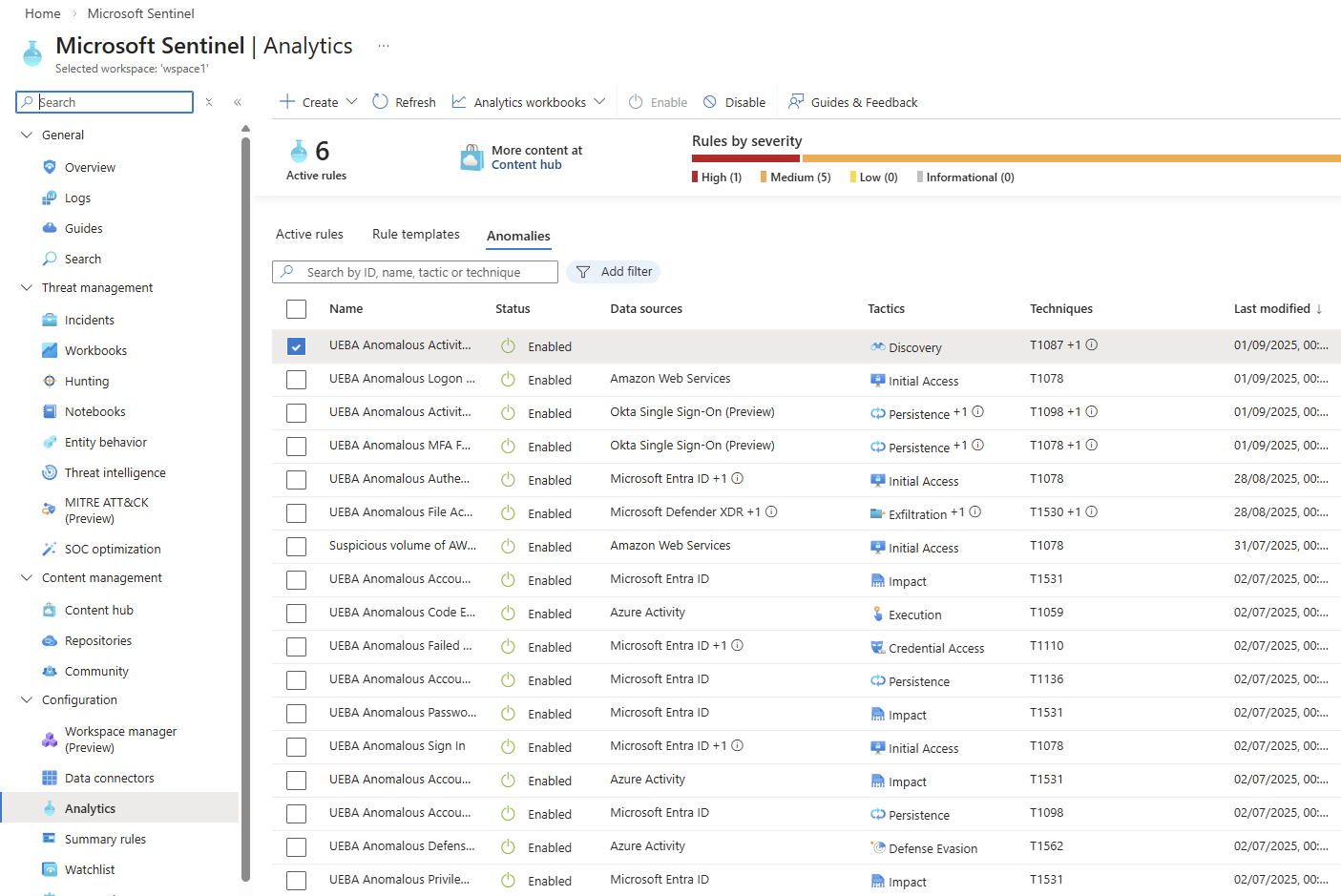
Part 3 — UEBA Enablement
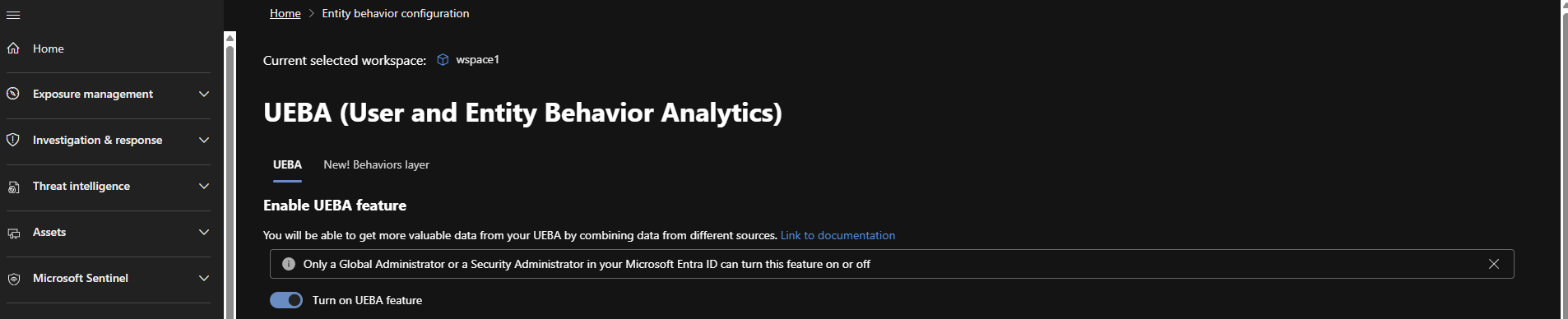
3.1 Enabling UEBA
Enabled User and Entity Behaviour Analytics to enhance detection capability.
3.2 UEBA Rules Activation
Confirmed that UEBA-related analytic rules are enabled.
Part 4 — Attack Simulation
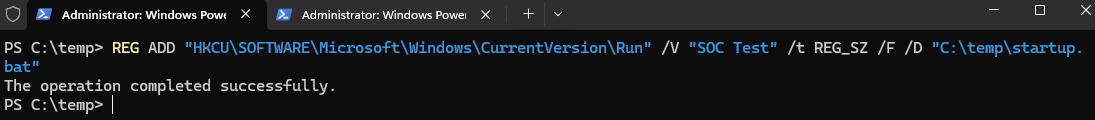
4.1 Persistence Simulation
Simulated persistence via registry modification.
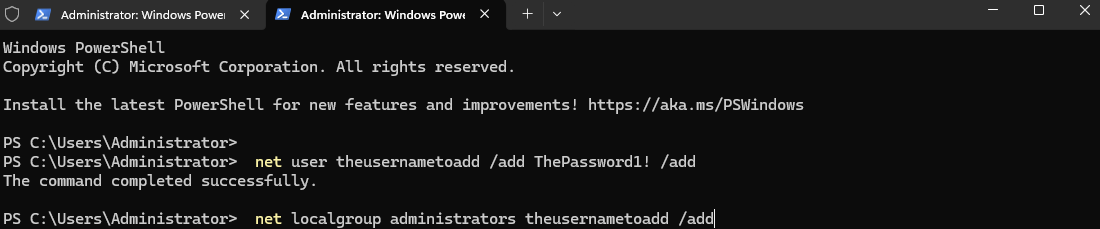
4.2 Privilege Escalation Simulation
Simulated user creation and privilege escalation activity.
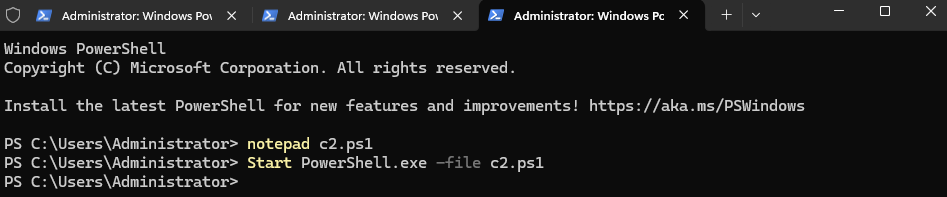
4.3 Command & Control (C2) Simulation
Simulated DNS-based C2 communication.
Part 5 — Detection Engineering
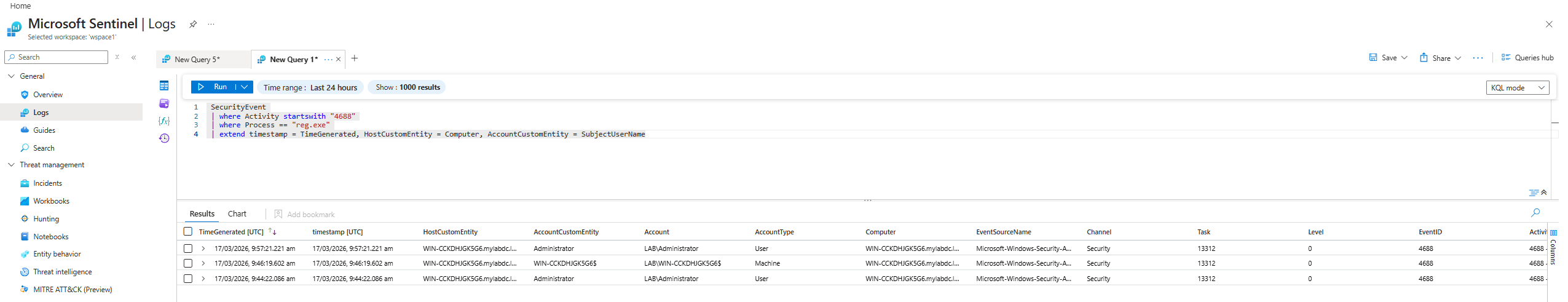
5.1 Persistence Detection Query
Developed a query to detect registry-based persistence.
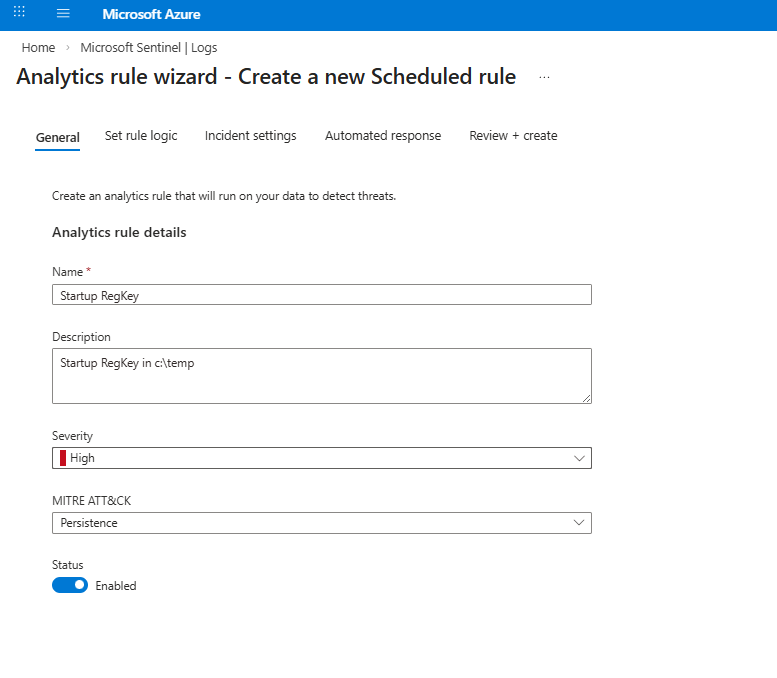
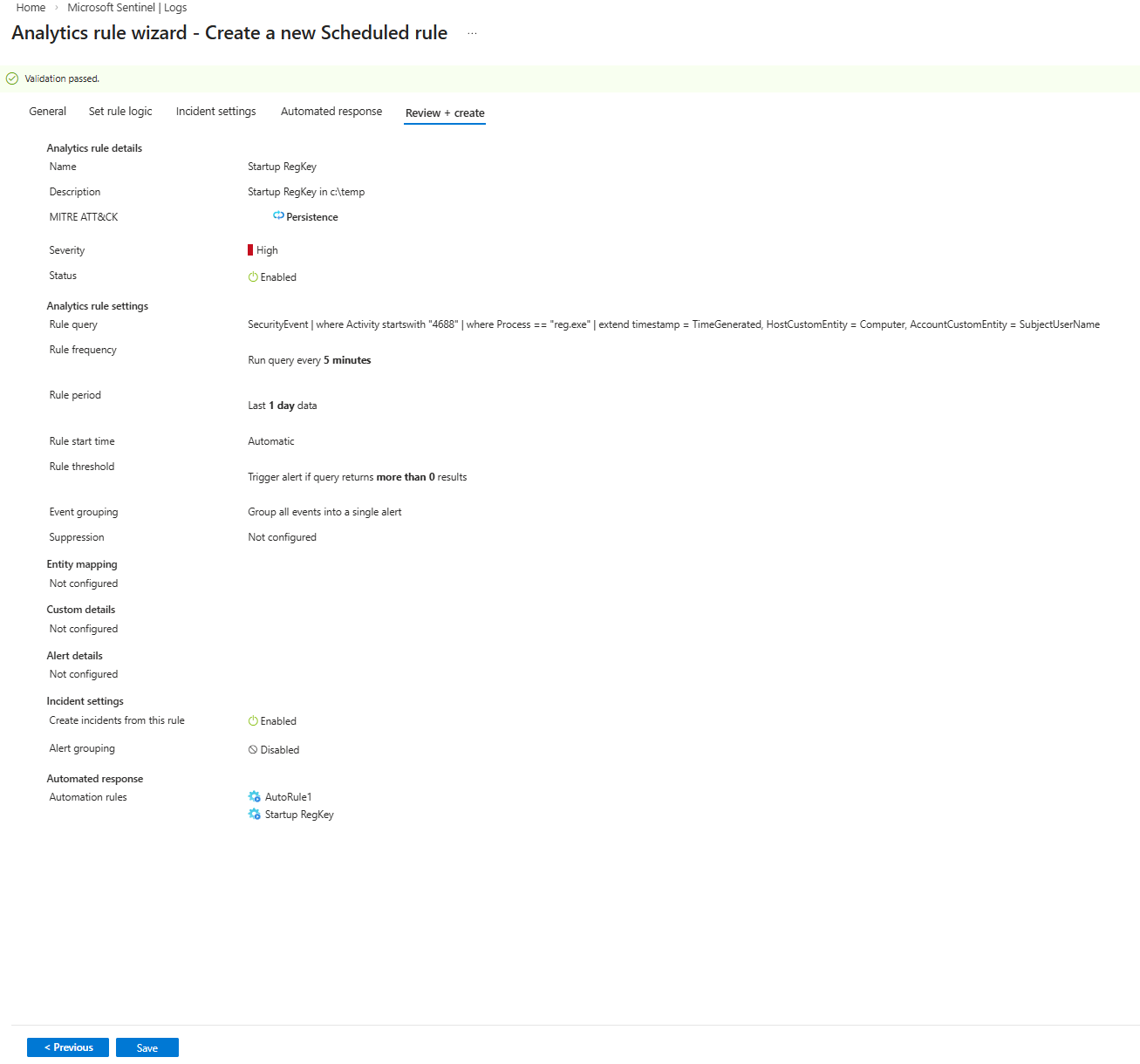
5.2 Detection Rule Creation
Created an analytic rule based on the persistence detection query.
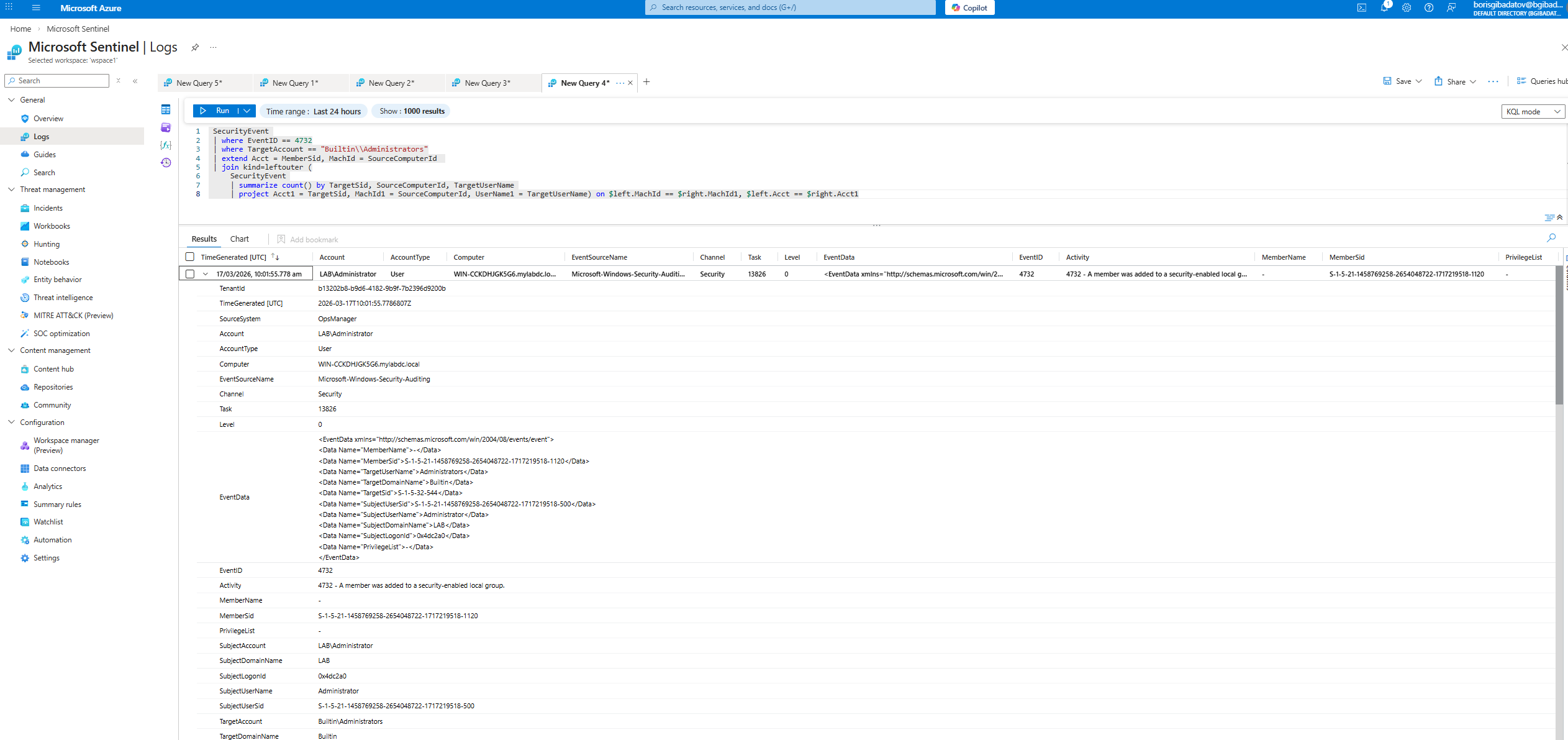
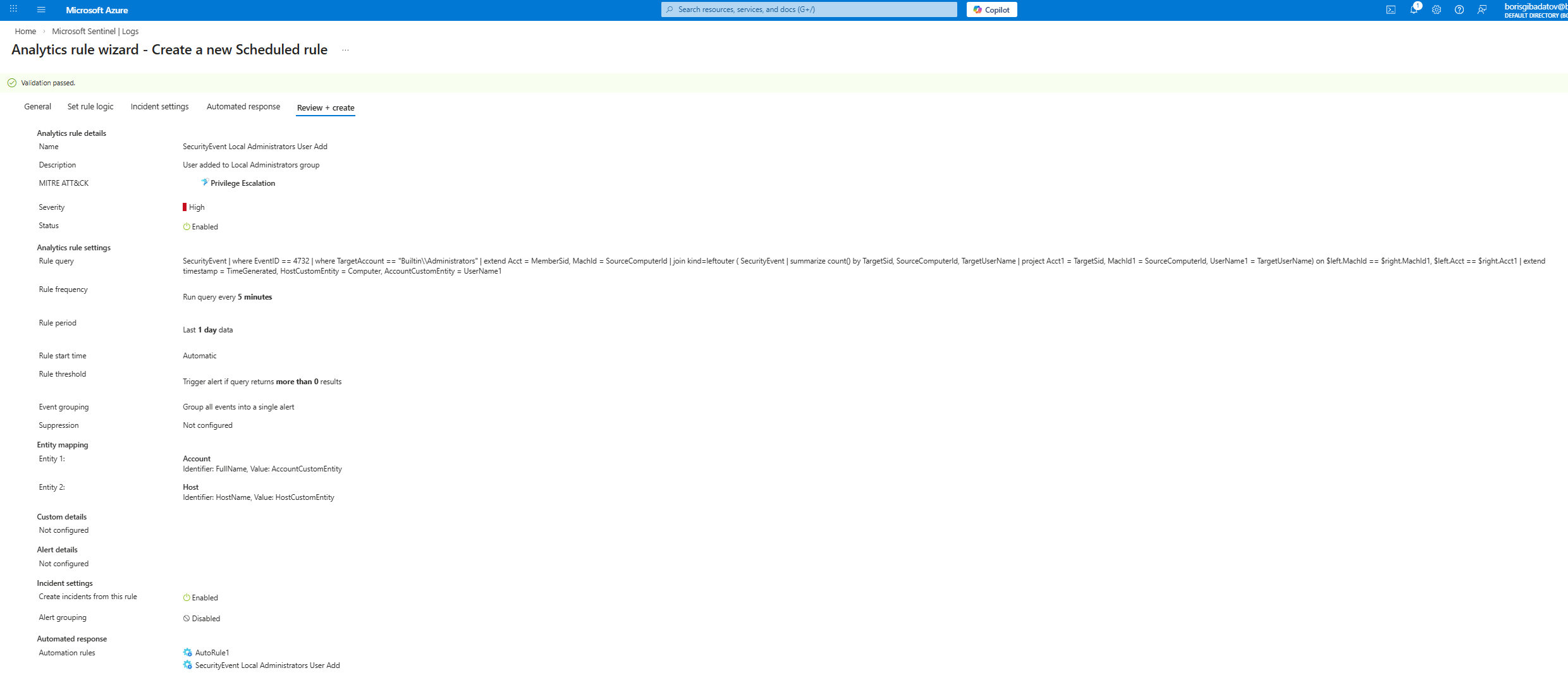
5.3 Privilege Escalation Query
Developed a query to detect group membership changes.
5.4 Privilege Escalation Detection Rule
Created detection rule to alert on privilege escalation activity.
Part 6 — Incident Investigation & Response
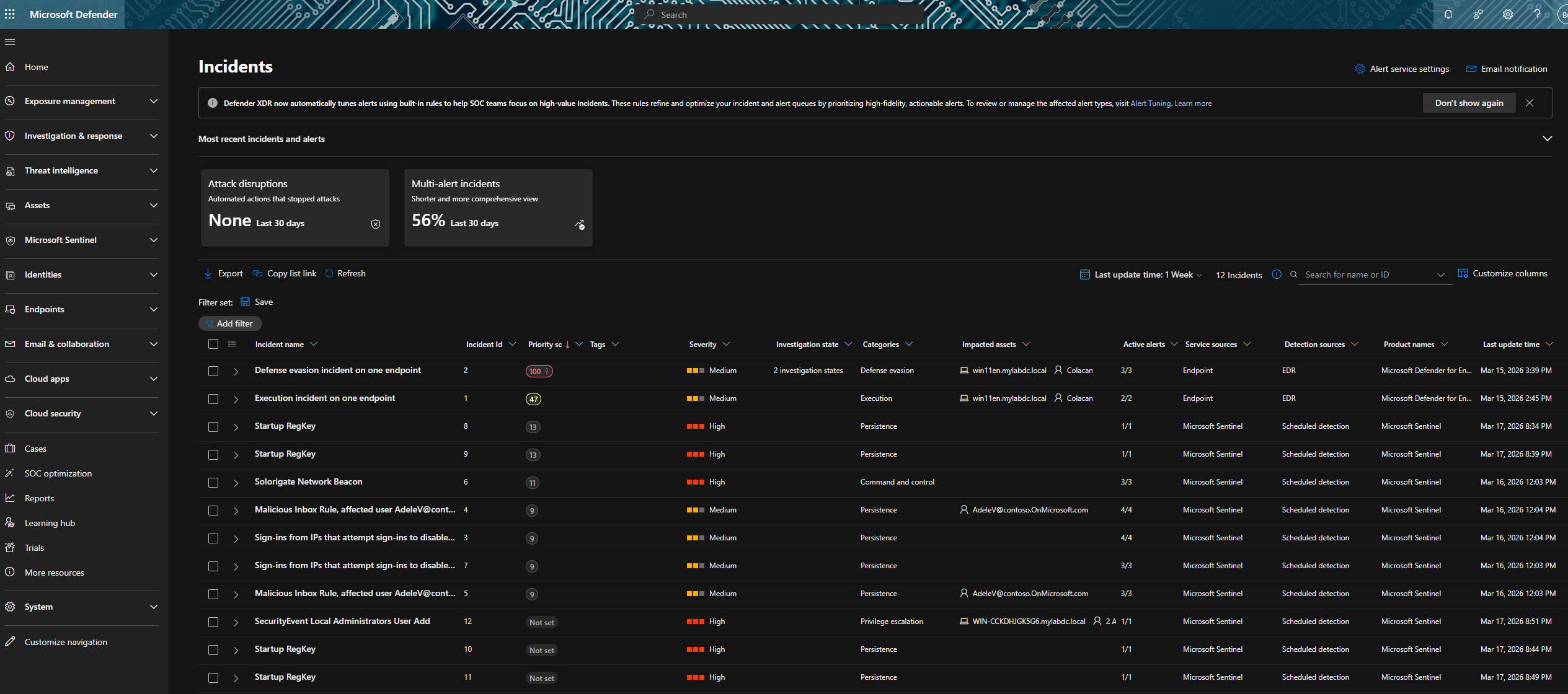
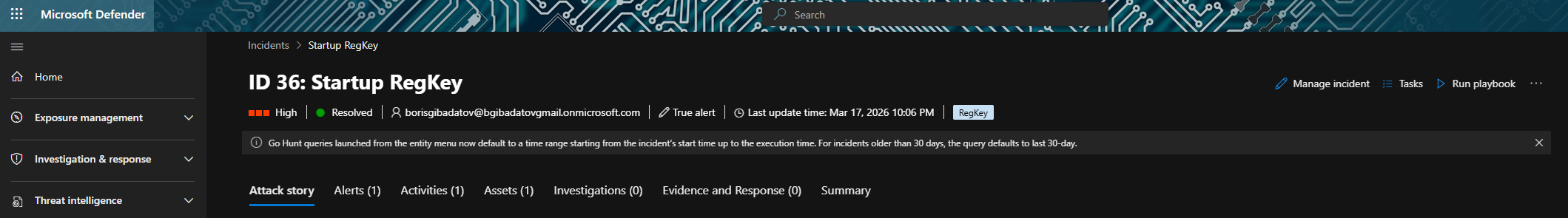
6.1 Incident Overview
Reviewed generated incidents in Microsoft Defender portal.
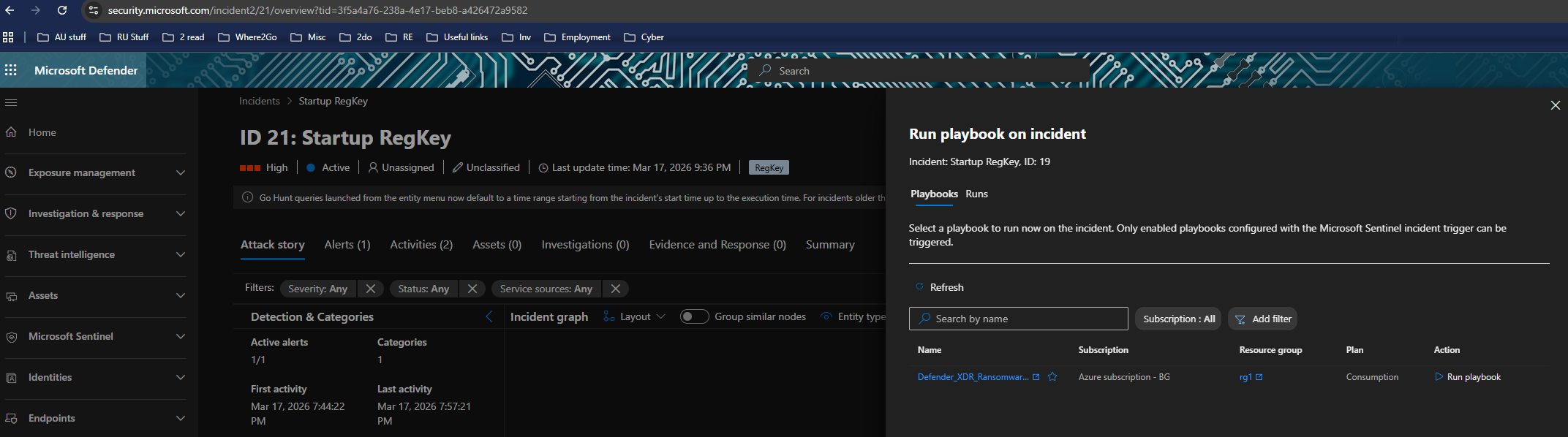
6.2 Playbook Execution
Executed playbook on selected incident.
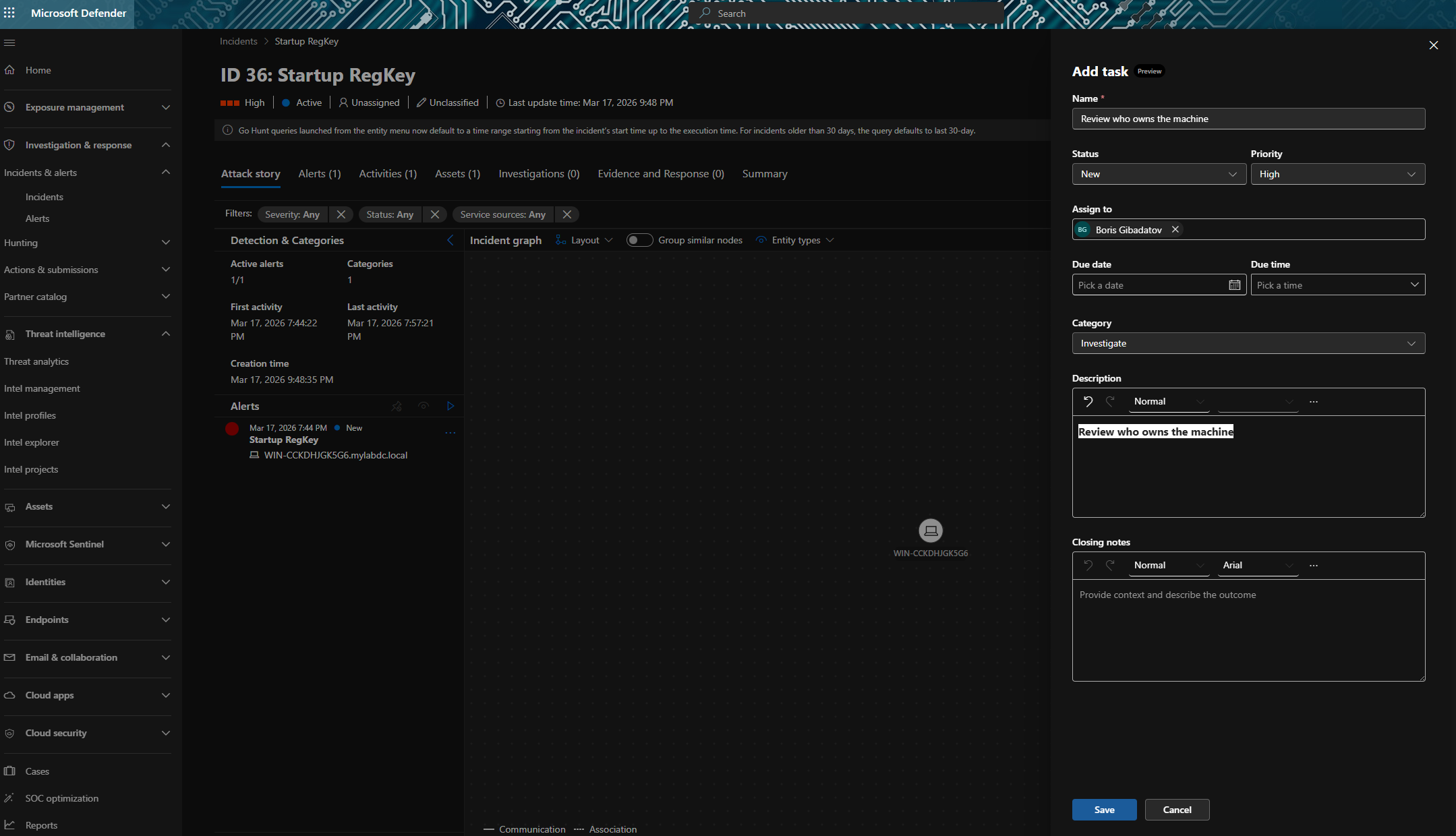
6.3 Task Creation
Created investigation task within the incident.
6.4 Incident Resolution
Updated incident status to resolved after investigation.
Investigation Value
This lab demonstrates a complete SOC workflow:
- Detection via analytics rules
- Alert correlation into incidents
- Automated response via playbooks
- Investigation and validation
- Incident closure
Skills Demonstrated
- Detection engineering in Microsoft Sentinel
- KQL-based analytics rule creation
- SOAR automation with playbooks
- UEBA integration
- Incident investigation and response
- End-to-end SOC workflow
Disclaimer
All activities were performed in a controlled lab environment using simulated attack scenarios.